
Multifactor Authentication
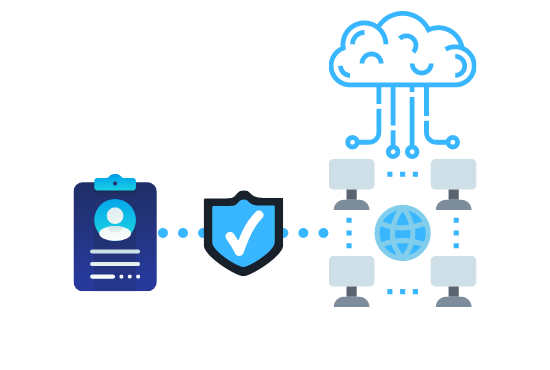
Multi-Factor Authentication (MFA) is a security system that verifies a user’s identity by requiring multiple credentials. It is a critical component of identity and access management (IAM). Rather than just asking for a username and password, MFA requires other—additional—credentials, such as a code from the user’s smartphone, the answer to a security question, a fingerprint, or facial recognition.

Identity Access and Management
Identity and access management is a critical part of any enterprise security plan, as it is inextricably linked to the security and productivity of organizations in today’s digitally enabled economy. A robust IAM system can add an important layer of protection by ensuring a consistent application of user access rules and policies across an organization.

SOAR Solutions
Security orchestration involves interweaving people, processes, and technology in the most effective manner to strengthen the security posture of an organization. Security Orchestration, Automation & Response (SOAR) technology will automate up to 95% of all response actions requiring human review and allow overloaded security teams to focus on the actions that really require their attention.
Network Access Control
Network Access Control (NAC) technology is a key driver to secure your Enterprise wired and wireless networks from unauthorized access. By providing dynamic network access based on user profiles and privileges is key to a successful deployment; understanding the key pain points in NAC integration with authentication, auto-remediation services, dynamic VLAN assignment based on endpoint compliance and reputation and designing the right solution is what differentiate One Network with our competitors.

Next Gen Firewalls
Next Generation Firewall (NGFW) can be described as the firewall which adds the protective layers such as application-level inspection, advanced level of intrusion protection system, and also adds intelligence to the boundaries of a traditional firewall along with the standard port/protocol protection.Improved detection of encrypted applications and intrusion prevention service. Modern threats like web-based malware attacks, targeted attacks, application-layer attacks, and more have had a significantly negative effect on the threat landscape.

Endpoint Security
Endpoint security is the act of making sure that endpoints or section purposes of end-client gadgets, for example, work areas, workstations, and cell phones from being abused by vindictive entertainers and battles are taken care of. Advanced Endpoint Security frameworks ensure these endpoints are on a system or in the cloud safely stored from cybersecurity dangers. Endpoint security has advanced from conventional antivirus programming to giving far-reaching assurance from modern malware and developing zero-day dangers.

Mobile, Email & Web Security
One of the biggest problems with email is that the messages are transmitted over the public internet. This means that it is theoretically possible for malicious parties to intercept email message transmissions and thereby gain access to what may be confidential information or data. The best way to avoid this is to use encryption to protect sensitive data when it is transmitted over the internet.

Cloud and DC Security
Cloud & Datacenter Security refers to a broad set of rules, technologies, applications, and controls used to protect virtualized IP, data, applications, services, and associated IT infrastructure in the cloud. It is a subdomain of computer security, network security and, more broadly, information security.

